- Swarm drones enhance defense operations through coordinated maneuvers and real-time data sharing.
- They excel in efficiency, covering vast areas rapidly for surveillance, reconnaissance, and targeted operations.
- Their adaptability allows autonomous response to dynamic threats, minimizing human intervention and risk.
“Autonomous swarm drones redefine defense strategy making traditional systems obsolete potential for rapid disruption and significant geopolitical impact.”
What Is the Tech Reality for Autonomous Swarm Drones?
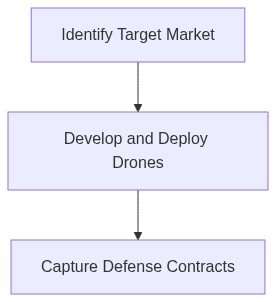
Swarm drone technology is not the future. It is now. The military and defense industries are on the brink of a significant overhaul driven by artificial intelligence, machine learning, and rapid sensor fusion. These drones operate in a coordinated group, making decisions collectively in real-time through decentralized algorithms. They possess the capability to outsmart centralized command-and-control structures. My focus is on companies that can demonstrate an operational Minimally Viable Swarm (MVS). This encompasses flight capabilities, real-time threat adaptation, and secure communication channels. I must also consider value chain innovations—such as novel propellants, materials for lightweight durability, and cybersecurity suites. I demand evidence of a clear technology advantage, like superior decision-making algorithms or enhanced hardware robustness, over competitors captured by verified case studies.
How Does the Monopoly Mechanism Capture Value?
It’s not just about having superior technology. The mechanism to capture value is more critical. The proprietary nature of algorithms and patents generates a defensible moat. Network effects manifest as each additional drone enhances the collective intelligence and effectiveness of the swarm. Integration with current military systems needs strategic partnerships and exclusive contracts with defense departments globally. I look for firms with government endorsements, certifications, or grants that increase trust and block competitors. Strategic rival acquisitions create synergy and reinforce market stronghold. They secure access to talent pools specializing in swarming algorithms or specialized hardware components. Monopoly is achieved through a data flywheel that improves decision-making and mission success rates rapidly as each mission collects more operational data.
Step 1 Conduct a Tech & IP Audit. Connect with an IP attorney specializing in AI and drones. Assess patents, licenses, and proprietary algorithms. Learn more on technology audits. Identify potential legal hurdles. Engage consultants to benchmark technology maturity via Technology Readiness Levels (TRL).
Step 2 Evaluate Target Military & Defense Channels. Leverage existing military contacts. Schedule briefings with Department of Defense tech liaisons to gauge their specific swarm operational requirements. Board as an observer on military technology advisory committees. Draft case study-based investment theses for top military adopters.
Step 3 Source Prime Targets. Utilize a private market database like PitchBook or CB Insights. Filter by keywords autonomous drones, swarm technology, AI-driven defense platforms. Ensure MVS functionality is at a minimum TRL 7. Review founders’ track records driven by technological pedigree and past defense alignments. Discard startups without cybersecurity measures hardwired into their product architecture.
Step 4 Perform Financial and Strategic Due Diligence. Analyze burn rate, runway, and underlying financial health. Underwrite the startup’s existing government contracts and partnerships—a critical revenue charting and risk management move. Explore synergy possibilities with existing defense portfolios. Reach out to other VC syndicate members to gauge interest level and potential co-investment dynamics.
Step 5 Draft an Investment Term Sheet. Structure for a win-win. Emphasize milestone-driven capital deployment, contingent on military contract execution or tech improvements. Include robust anti-dilution and veto rights for pivot strategies focused on non-defense markets, maintaining portfolio security as the pivot occurs.
Step 6 Develop Go-to-Market Strategies Post-Investment. Collaborate with their marketing team to document success stories for targeted PR campaigns. Engage with military technology expos and exclusive defense summits to ensure high visibility. Enable accelerated user experience feedback loops via deployed military sectors.
Step 7 Execute a Conglomerate Exit Pathway. Design an exit strategy focusing on merger/acquisition interest from established aerospace and defense behemoths. Ensure high due diligence visibility through strategic alliance showcases. Participate in competitive tender invitations regularly. Consider IPO event monitoring based on market windows and political stabilizations.
| Attribute | Details |
|---|---|
| CapEx (Year 1) | $70M – Pilot Deployment |
| CapEx (Year 2-5) | $300M – Scale Operations |
| CapEx Allocation | R&D 40%, Manufacturing 30%, Marketing 20%, Misc. 10% |
| TAM (Initial) | $1.2B – Defense Contracts |
| TAM (3-Year Projection) | $5B – Multi-Sector Expansion |
| TAM Drivers | Increased Global Defense Budgets, Technological Integration |
